What follow is how to set up as SSH tunnel using PuTTY with the MySQL port (3306) forwarded as an example. After completing this how-to you'll have port 3306 on your local machine listening and forwarding to your remote server's localhost on port 3306. Thus effectively you can connect to the remote server's MySQL database as though it were running on your local box.
This how-to assumes your MySQL installation has enabled listening
to a TCP/IP connection. Only listening on 127.0.0.1 is required
(and the default as of MySQL 4.1). Although beyond the scope of this
how-to, you can verify the server's listening by using mysql
-h 127.0.0.1 rest of options on the server. Look for
bind-address = 127.0.0.1 and skip-networking = 0
in your /etc/mysql/my.cnf. Also, a
trouble-shooting guide.
To achieve the same with PostgreSQL simply use PostgreSQL's default
port, 5432. psql -h 127.0.0.1 rest of options
to test; /etc/postgresql/pg_hba.conf and the manual
as pointers for configuration.
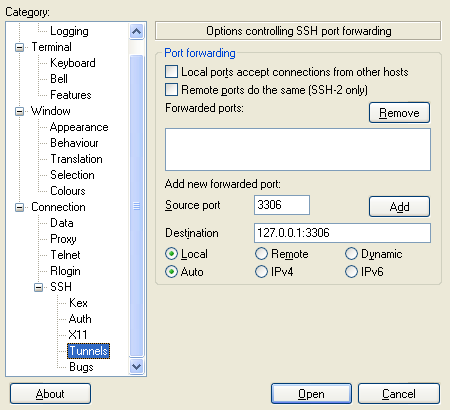
Create a session in PuTTY and then select the Tunnels tab in the SSH section. In the Source port text box enter 3306. This is the port PuTTY will listen on on your local machine. It can be any standard Windows-permitted port. In the Destination field immediately below Source port enter 127.0.0.1:3306. This means, from the server, forward the connection to IP 127.0.0.1 port 3306. MySQL by default listens on port 3306 and we're connecting directly back to the server itself, i.e. 127.0.0.1. Another common scenario is to connect with PuTTY to an outward-facing firewall and then your Destination might be the private IP address of the database server.
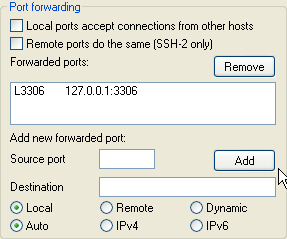
Click the Add button and the screen should look like this,
Unfortunately PuTTY does not provide a handy ubiquitous Save button on all tabs so you have to return to the Session tab and click Save,
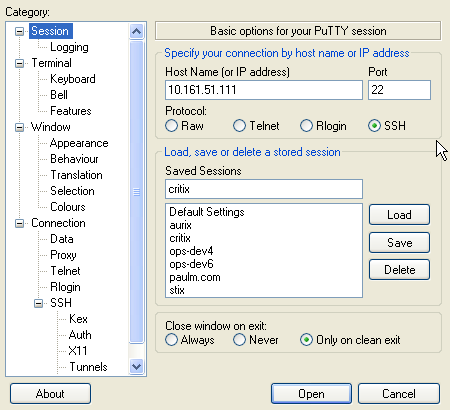
Click Open (or press Enter), login, and enjoy!
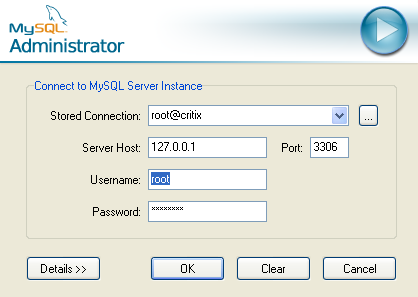
Here for reference is an example connection using MySQL Adminstrator going to localhost: note the Server Host address of 127.0.0.1 which will be transparently forwarded.